I recently went through the 350 or so reviews of the BofA iPhone app. Here are my conclusions.
First of all, BofA should have called this app “ATM locator” instead of “Mobile Banking”, as the ATM locator capability is praised by most as a way to save on fees when traveling out-of-town or when in unfamiliar neighborhood, but the overwhelming majority comment on the fact that the application provides a very poor mobile banking experience on the iPhone.
What is meant by iPhone-specific experience?
iPhone-specific experience is the single most requested feature. I’m careful not to talk about implementation details here (native app versus iPhone-optimized Web app) as I still don’t have a strong opinion about which approach would ultimately bring the best user experience (native app developed in-house would require a learning curve that would certainly impact the quality of the app, while a Web app would have to be provided with JavaScript API wrappers of some of the SDK APIs like CoreLocation to provide an interesting user experience).
For most what iPhone-specific experience means is:
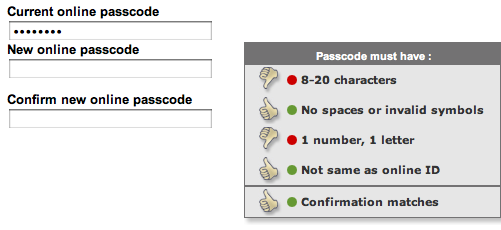
- More finger-friendly (avoid pinching, which is a sign that the app is not optimized for the iPhone)
- iPhone-specific styling like buttons instead of tiny text-based links
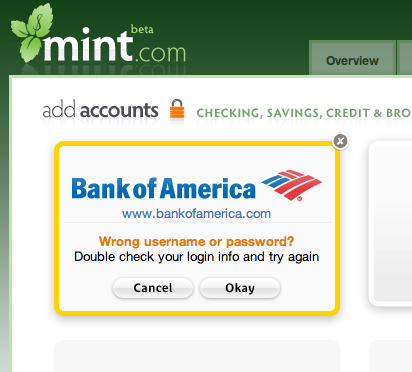
- Consistency across the whole app (not a mix of a native for ATM locator and Web for mobile banking that does not instill confidence)
- More condensed information per page using table views
Other interesting requested features
Here are the other interesting features requested:
- Add support for customers in Washington and Idaho states.
- Faster login (one suggested using a PIN instead of a long password)
- Transaction reconciliation via mobile banking
- Background download of information such as balance for quick one-click look
- Better support for credit card accounts (currenly only balance is available, not transaction list)
- Support for My Portfolio feature
- “Something like E-Trade on the BlackBerry”.
Further thoughts: personalizing the mobile banking experience
The one thought that came out of this analysis was that mobile users have fundamentally different needs in terms of the information they want to see after clicking the BofA logo on the iPhone homescreen.While most expect to be able to do everything they can do with online banking, all expect to do much faster the things they do most commonly in online banking. And that’s where the design problem of shrinking online banking into a mobile app is in my opinion. On one hand, what everyone does most commonly is very different from customer to customer. On the other hand, an intuitive interface design principle is “Human interface cognitive load is proportional to the number of clicks/keystrokes/gestures“, which means that people won’t like the user experience unless they get to do what they want to do in the least number of clicks and keystrokes. This includes login in, selecting a transaction, entering amounts, etc.
To give a few examples from the reviews: those who travel don’t care about the ATM locator. Those who travel love it. Some only have a Credit Card account with Bofand don’t care about Checking/Savings.
Which leads me to think that the future of the BofA iPhone app or any mobile banking app for that matter will be in the ability for the user to personalize their experience by providing to BofA the shortcuts to the transactions they do most.
This may include just a transaction identifier and an account identifier (ex. “view balance” “checking-1234″) or more complex shortcuts that borders on programming/querying: for instance “view transactions” “CC-8456″ “Last 10 posted transaction” or “transfer” “$100″ “to John”.
Online banking will most likely be the place where these personalizations will be programmed. Until then, getting that 5 star rating on iTunes app store and getting everyone happy might be difficult.